Posts by Jerry Sheehan
What is internet surveillance in 2025?
In 2025 almost 70% of American homes have at least one device connected to the internet. This makes the web of Internet surveillance very complex and widespread. Even simple online actions are not private; from the 264% increase in U.S. law enforcement requests to Amazon to a Fitbit’s heart rate data leading to a murder…
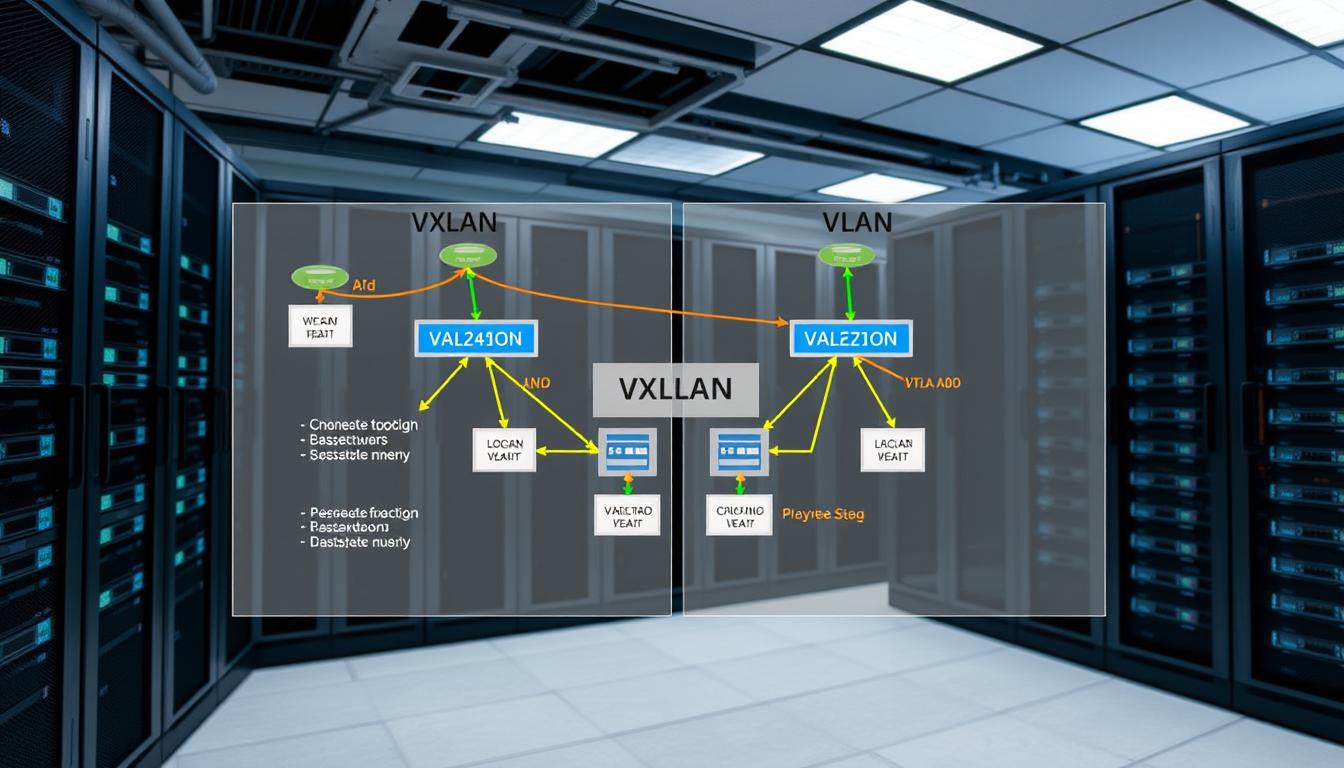
Read MoreVXLAN vs VLAN: Comparison and Key Differences
Did you know VLANs have a 12-bit ID space? This limits them to 4,096 segments. On the other hand, VXLAN uses 24 bits for its ID. This allows up to 16 million segments. We’re going to compare vxlan vs vlan. We’ll see how VXLAN solves scalability problems. Both technologies divide networks, but VXLAN does it…
Read More10 Key Functions of an Operating System Explained.
Did you know today’s computers and smart devices run over 100 million lines of code daily? At the heart of this complex system is the operating system. It’s the key to understanding what is an operating system and its essential roles in modern computing. An operating system is more than software. It’s a vital manager…
Read MoreUnderstanding VTY lines in Network Configuration
A single Cisco router can have up to 21 virtual terminal lines. This lets many administrators work together. Network teams use these lines to manage devices securely. They can grant access to certain users or block others. For example, they might allow a level 15 username to access but block 10.1.1.3/24 from telnet sessions. vty…
Read MoreComputer Architecture: Key Concepts and Principles Explained
In 1936, the first computer architecture was documented. This was 23 years before the term became common. It shows how fast technology advances in our digital world. CPU latency for disk storage is in milliseconds. Cache works in nanoseconds. This big difference shows why a clear plan is key. It helps hardware and software work…
Read MoreWhat Is SVM? Understanding Support Vector Machines.
Did you know the svm algorithm has been key in image recognition and text analysis for years? It’s why researchers worldwide use it to sort spam and detect fraud. Introduced in 1963 by Vladimir N. Vapnik and Alexey Ya. Chervonenkis, it gained fame in the 1990s. This approach aims to find the best boundary, or…
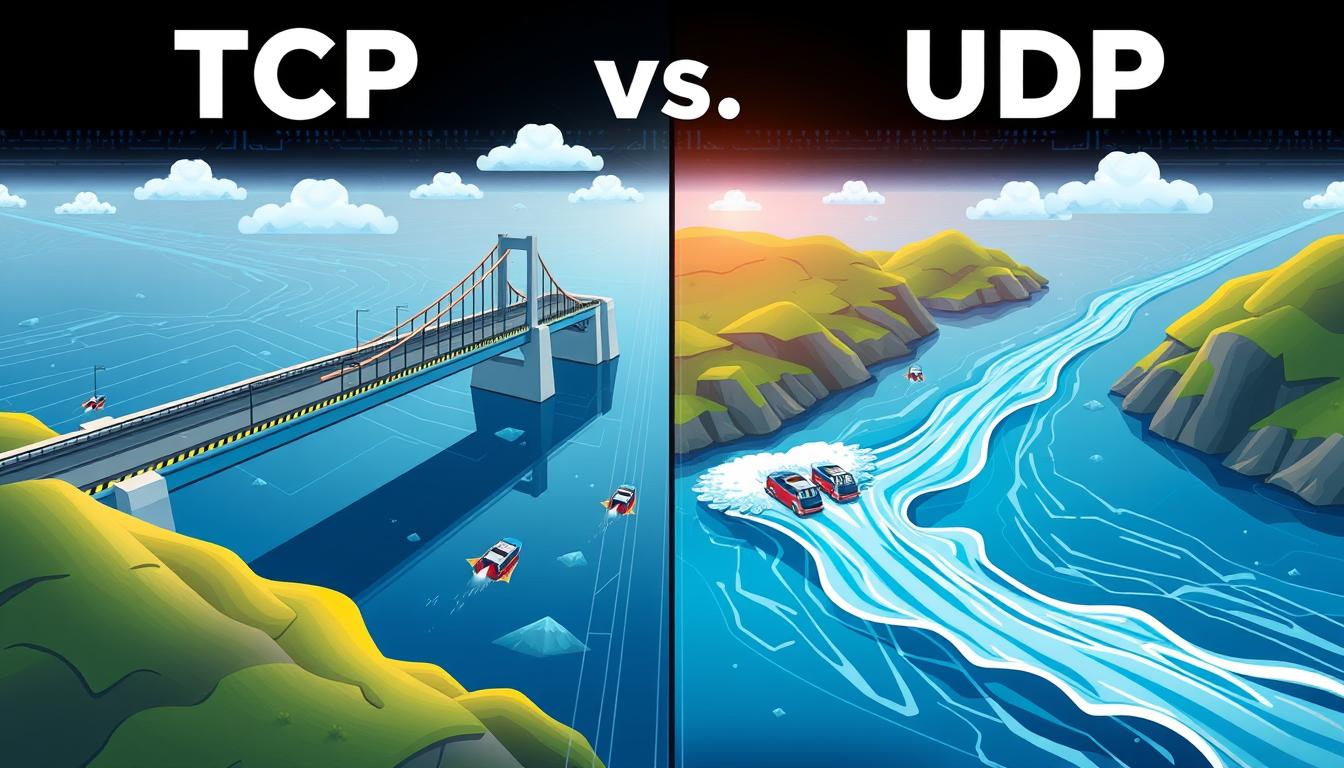
Read MoreTCP vs UDP: Differences and When to Use Each
It takes three steps to start sending data over TCP. But UDP does it all without a handshake. This shows how TCP and UDP work differently in networks. TCP makes sure data is reliable by checking for errors. But this makes it slower. UDP, on the other hand, sends data fast, even if some gets…
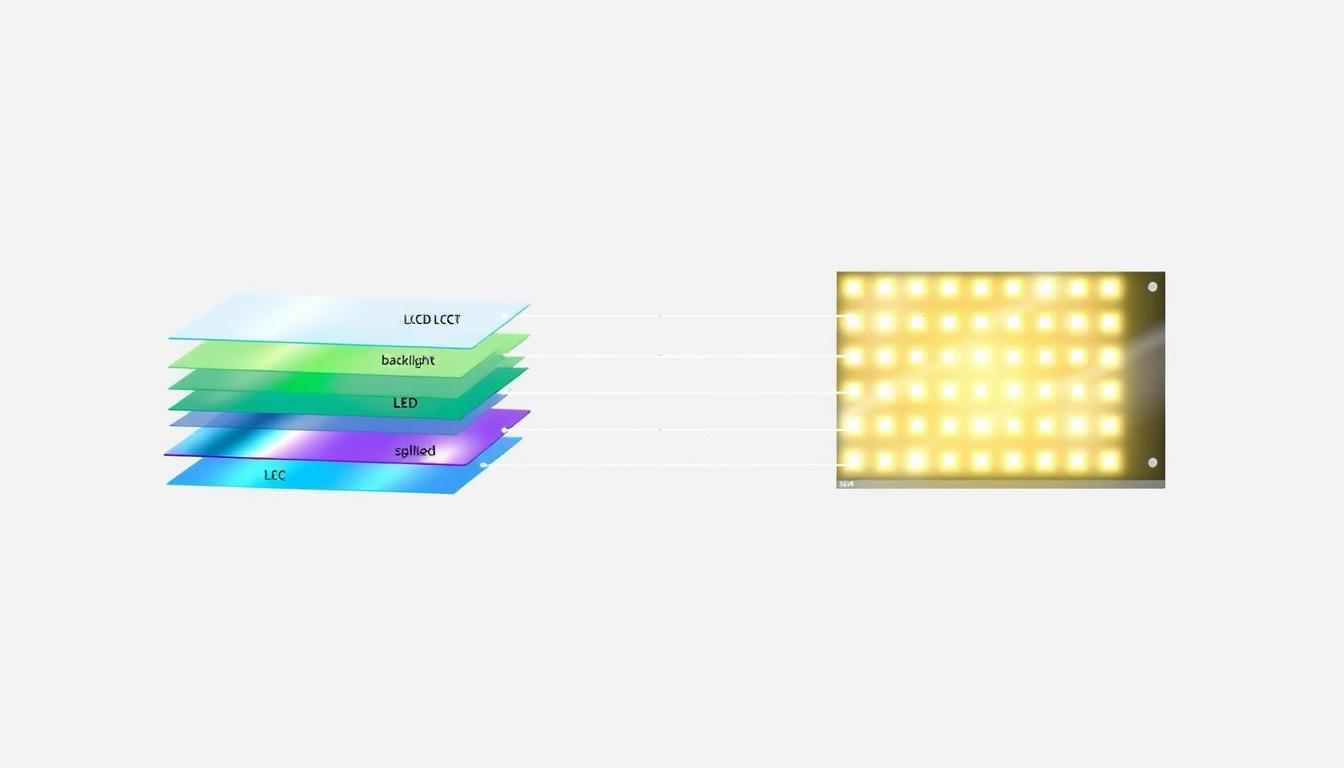
Read MoreLCD vs LED: Key Differences and Which Display Is Better
Did you know LED screens can deliver black levels up to 100% better than older LCD screens? This fact has led to many debates about lcd vs led. Viewers want sharper, more vibrant images. Both displays are great at showing clear visuals. But they use different backlighting methods. We’ll look into the led vs lcd…
Read MoreIP Mask: The Ultimate Guide to Hiding Your IP Address
Did you know that nearly 50% of VPN users cite privacy and security as their primary reasons for hiding their online identity? In today’s digital age, protecting your network activity is more important than ever. One of the most effective ways to achieve this is by using an IP mask. An IP mask is a…
Read MoreESX vs ESXi: Unveiling Key Differences & Features
VMware ESXi shows a 10% to 14.5% better performance than Proxmox in CPU and memory use. This highlights a key difference between ESX and ESXi. Efficiency is a big factor in choosing between them in IT settings. VMware started with ESX, a strong service console. But, as needs changed, VMware updated to ESXi. ESXi is…
Read More