Network & Infrastructure
Understanding Infrastructure as Code Explained: What Is Infrastructure as Code
About 80% of global IT teams plan to use code-driven provisioning in the next two years. This marks a move from manual setup to a more efficient method called infrastructure as code. This approach, also known as iac infrastructure as code, lets teams write server setups and network resources in files. It makes things more…
Read MoreUnderstanding YAML Files: A Simple Guide – What Is a YAML File
Did you know over half of DevOps engineers use yaml files every day? This format is loved for its simple structure. It uses indentation, not complicated brackets, making it easy to read. Yaml files keep data organized, making it easier for teams to work together. They balance human readability with machine instructions. Yaml files are…
Read MoreUnderstanding Webhooks: A Quick Guide
More than half of online platforms use real-time alerts to keep users connected. This focus on instant updates highlights the importance of webhooks. A webhook is a quick signal that one app sends to another when an event happens. Many wonder, “What is a webhook?” or “What are webhooks?” They make data flow automatic, without…
Read MoreUnderstanding TCP Traffic: Insights & Tips
The Transmission Control Protocol (TCP) is key to the internet’s data exchange. It handles billions of packets every second. This keeps devices connected all over the world. TCP makes sure packets arrive in the right order. It uses details like timestamps, ports, and flags for secure communication. It shows how analyzing these can uncover hidden problems.…
Read MoreUnderstanding the IPv4 Header Structure
Over four billion IPv4 addresses are in use today. This shows how widespread this protocol is. Each ip packet starts with an ipv4 header. This header has important fields that help data move across networks. Experts use it to make sure data gets to the right place. IPv4 is a connectionless protocol. It doesn’t guarantee…
Read MoreUnderstanding IPsec for Secure Networks
About seven out of ten organizations use encryption for important data. This shows the growing need for better security in online communication. So, what is ipsec? It’s a set of protocols that encrypt and authenticate packets in networks. The Internet Engineering Task Force created it to fight against eavesdropping and cyberattacks. It acts as a…
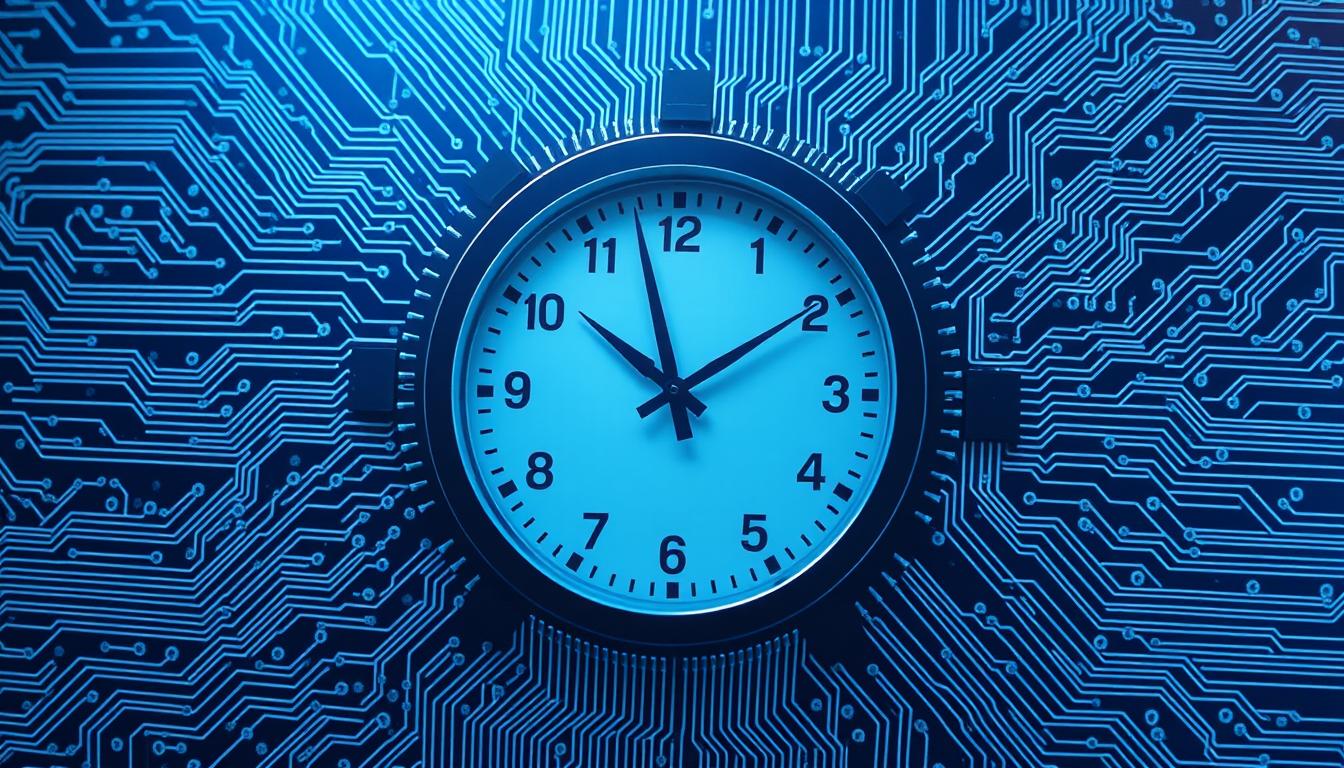
Read MoreMastering Precision Time Protocol – Essential Guide
Did you know a timing error of just a few nanoseconds can disrupt critical data exchanges in global trading rooms? This tiny margin shows why experts rely on the precision time protocol, or ptp. It’s the key to consistent synchronization. PTP’s importance has grown as industries need split-second accuracy. This ensures they stay efficient. Modern…
Read MoreUnderstanding Route Reflector Benefits in BGP
In big networks, having an iBGP full mesh means lots of peerings. A single route reflector greatly reduces this, saving a lot of effort and bandwidth. A bgp route reflector makes it easier for peers to share routes. It does this without needing every device to connect with each other. This section shows how it…
Read MoreInter VLAN Routing Explained for Network Pros.
It might surprise you to learn that nearly three out of four network outages are caused by weak segmentation. This shows how important a good VLAN design is. Inter vlan routing makes it easy and safe to share data between different segments. Data from <web_sourse> shows that intervlan routing is key for letting traffic move…
Read MoreEnable SSH on Cisco Devices – Quick Guide to Cisco enable SSH
Did you know over 70% of targeted attacks target unsecured remote access points? This shows how important encrypted connections are in network management. Secure Shell, or SSH, secures your Cisco devices and keeps data safe from unauthorized access. In this quick guide, you’ll learn how to create RSA keys and use a Cisco crypto image…
Read More