Read the IT Support Blog

Cybersecurity Insurance in 2026 is Getting Harder to Get. Is Your Business Actually ‘Insurable’?

Volunteers, Board Members and Data Leaks: How to Secure Your Nonprofit’s ‘Revolving Door’

Tax Season IT Challenges: Solving for 4 Pressure Points on Your Infrastructure

Why GDPR Compliance Matters in Western New York: Managing Data Privacy for a Global Marketplace

Protect Patient Trust: Navigating HIPAA Compliance Standards in Buffalo and WNY

The CEO’s Guide to NIST Cybersecurity Compliance in Western New York: Why Alignment is Your New Insurance Requirement

The Competitive Edge: A CEO’s Guide to Using CMMC Services in Western New York
What You’ll Discover in Our IT Support Blog:
- Expert Guidance: Learn from our IT consultants about the best practices for managed IT services through the IT Support Blog.
- Cybersecurity Tips: Protect your business with actionable advice on data security and ransomware defense, shared in our IT Support Blog.
- Cloud Insights: Discover the benefits of cloud computing and how it can enhance your operations by exploring our IT Support Blog.
- Business Continuity: Prepare your organization for unexpected disruptions with continuity strategies featured in the IT Support Blog.
- Microsoft Support: Optimize your tools with in-depth guides and troubleshooting tips provided in the IT Support Blog.
Each post in the IT Support Blog is carefully crafted to provide practical, real-world solutions that empower your business to thrive in today’s tech-driven landscape. Our IT Support Blog features articles tailored to both beginners and IT professionals, ensuring there's something for everyone.
Explore Our IT Support Blog
Browse through our curated collection of posts in the IT Support Blog, neatly organized in a grid layout for easy navigation. Each article in the IT Support Blog offers actionable insights, step-by-step guides, and innovative strategies to address your IT support challenges. Bookmark the IT Support Blog page and stay updated with fresh content added regularly.
Why Follow Our IT Support Blog?
- Stay informed on the latest IT trends and updates with the IT Support Blog.
- Gain access to expert solutions tailored for small and mid-sized businesses by reading the IT Support Blog.
- Learn how to leverage technology to streamline your operations, guided by the articles in our IT Support Blog.
Explore the SynchroNet IT Support Blog today and uncover the tools and strategies you need to enhance your IT systems and achieve business success!
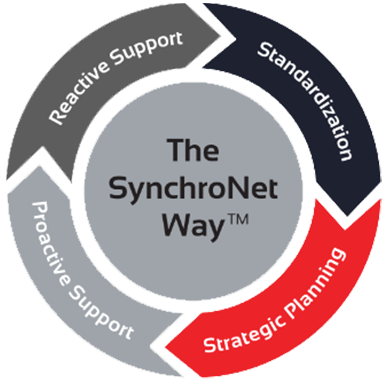
The SynchroNet Way
Want to move your business IT from the wild, wild West to an island of serenity? We get it, and we’ve helped transform everyday work life for hundreds of clients using The SynchroNet Way.
With our approach you get:
-
Standardization and a 100-point Best Practices checklist assigned to a dedicated network administrator.
-
Strategic planning at an executive level with a dedicated vCIO that keeps you on track for the long run.
-
Proactive support that monitors and protects your systems around the clock.
-
Reactive support from our friendly and caring customer support team who are always on the lookout for repeat issues.