Read the Blog

What Are the IRS Security Six Protocols
Maintaining a comprehensive security strategy to keep your customers’ data safe should be your number one priority as a business...

What Your Business Needs to Know About CMMC
Starting this year (in 2020) The United States Department of Defense is rolling out the Cybersecurity Maturity Model Certification (or...

Tips to Clean and Optimize Your Networks and Work Computers
To keep your networks and systems running as smoothly as possible, you will need to maintain and optimize them year-round....

How to Improve Your Organization’s Network Performance
A slow network can kill your business. Important calls could drop in the middle. Cloud applications can take longer to...

A View of COVID-19’s First Wave of Cybersecurity
COVID-19 changed the world in ways we never thought possible. While this pandemic hit us with new and seemingly insurmountable...

NIST Password Security Standards for 2020
The NIST (National Institute of Standards and Technology) works with federal agencies to set their security and password standards. They...

Why Running an Unsupported OS Is a Terrible Idea
CentOS reaches the end of its life cycle in November. The question that organizations that run it and other operating...
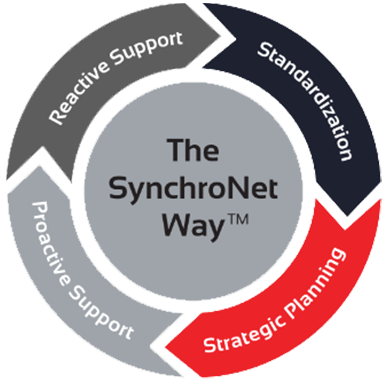
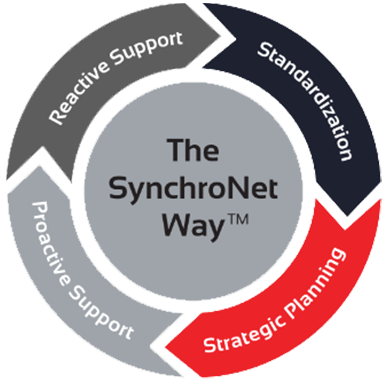
The Way
Want to move your business IT from the wild, wild West to an island of serenity? We get it, and we’ve helped transform everyday work life for hundreds of clients using The SynchroNet Way.
With our approach you get:
-
Standardization and a 100-point Best Practices checklist assigned to a dedicated network administrator.
-
Strategic planning at an executive level with a dedicated vCIO that keeps you on track for the long run.
-
Proactive support that monitors and protects your systems around the clock.
-
Reactive support from our friendly and caring customer support team who are always on the lookout for repeat issues.