Read the Blog

5 Easy Steps to Increase IT security
IT security is so crucial while living in today’s digital age. New tactics are being created by attackers all the...
Why is 2FA so Important?
Two factor authentication, or 2FA, is a growing necessity for anyone that cares about security. It’s a relatively new addition...

IT Security: Policies and Technologies
When it comes to IT security there is no 100% sure solution. We all wish that we could install one...

5 Essential IT Services You Should Get From an MSP
Outsourcing IT is becoming a more popular option than ever to help businesses that need affordable and effective IT solutions....

The True Value of hiring an MSP
There are many ways to find answers to your IT problems. The old model was typically to have an IT...

Who’s to Blame After a Malware Attack?
Malware attacks are something we all have to be concerned about. Everyone is vulnerable and it can be very easy...
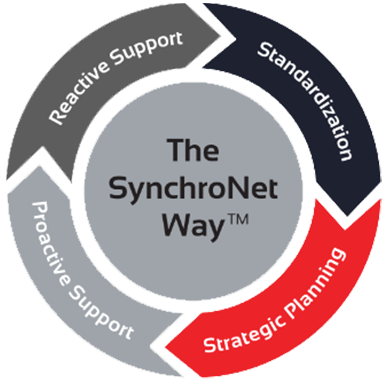
The Way
Want to move your business IT from the wild, wild West to an island of serenity? We get it, and we’ve helped transform everyday work life for hundreds of clients using The SynchroNet Way.
With our approach you get:
-
Standardization and a 100-point Best Practices checklist assigned to a dedicated network administrator.
-
Strategic planning at an executive level with a dedicated vCIO that keeps you on track for the long run.
-
Proactive support that monitors and protects your systems around the clock.
-
Reactive support from our friendly and caring customer support team who are always on the lookout for repeat issues.